Authorization & Access Control Infrastructure for Developers
Enforce user roles and permissionsSecure data across multi-tenant appsImplement fine grained access controlGate paid features behind pricing tiersEnforce attribute based access controlSimplify org and team managementEnforce policy based access control
Centralized Authorization, Globally Distributed
Define your authorization model once, enforce it anywhere. Warrant unifies authorization across microservices, frontend applications, cloud environments, edge runtimes, and more.
From Our Blog
Zanzibar: Google's Consistent, Global Authorization System
A deep-dive into Google Zanzibar, covering its key concepts and its strengths and weaknesses.
Why Google Zanzibar Shines at Authorization
Our CTO explores what makes Google Zanzibar especially compelling for building application authorization.
Understanding Relationship Based Access Control (ReBAC)
A deep-dive into Relationship Based Access Control, covering what it is, when/why to use it, and its pros/cons.
World-Class Developer Experience
Robust, well-documented APIs, intuitive SDKs, drop-in embeddable components, and a powerful CLI make up the backbone of an authorization platform developers love and rely on to serve millions of requests each day.
1#2# Check that user is not viewer of document.3#4warrant check \5 user:c88b7d viewer document:product-roadmap --assert false6
7#8# Assign user as viewer of document.9#10warrant assign \11 user:c88b7d viewer document:product-roadmap12
13#14# Check that user is now viewer of document.15#16warrant check \17 user:c88b7d viewer document:product-roadmap --assert true18
19
20
1//2// App.jsx3//4<WarrantProvider clientKey="<your_client_key>">5 {/* Routes, ThemeProviders, etc. */}6</WarrantProvider>;7
8//9// MyComponent.jsx10//11<ProtectedComponent12 warrants={[{13 objectType: "myObject",14 objectId: object.id,15 relation: "viewer",16 }]}17>18 <MyComponent/>19</ProtectedComponent>20
Server-side Authorization
SDKs for the most popular back-end languages & frameworks like Express, Go, Python, Java, and Ruby to add permission checks to your back-end API routes and business logic.
Complete Platform for Authorization
With tools built for developers, IT administrators, and even sales & customer support, Warrant is a complete platform for authorization across internal and customer-facing use cases.
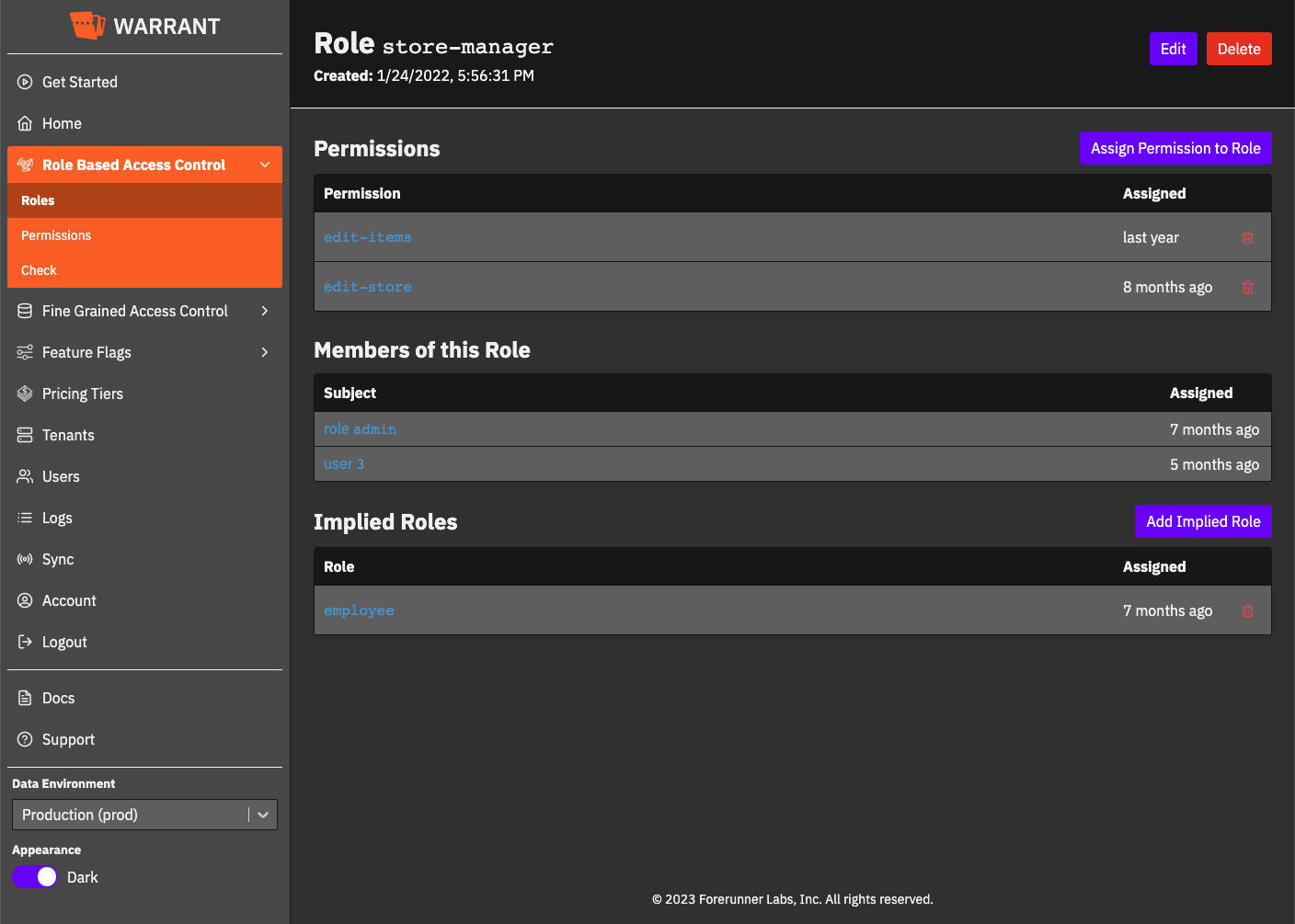
Roles & Permissions
Pricing Tiers & Entitlements
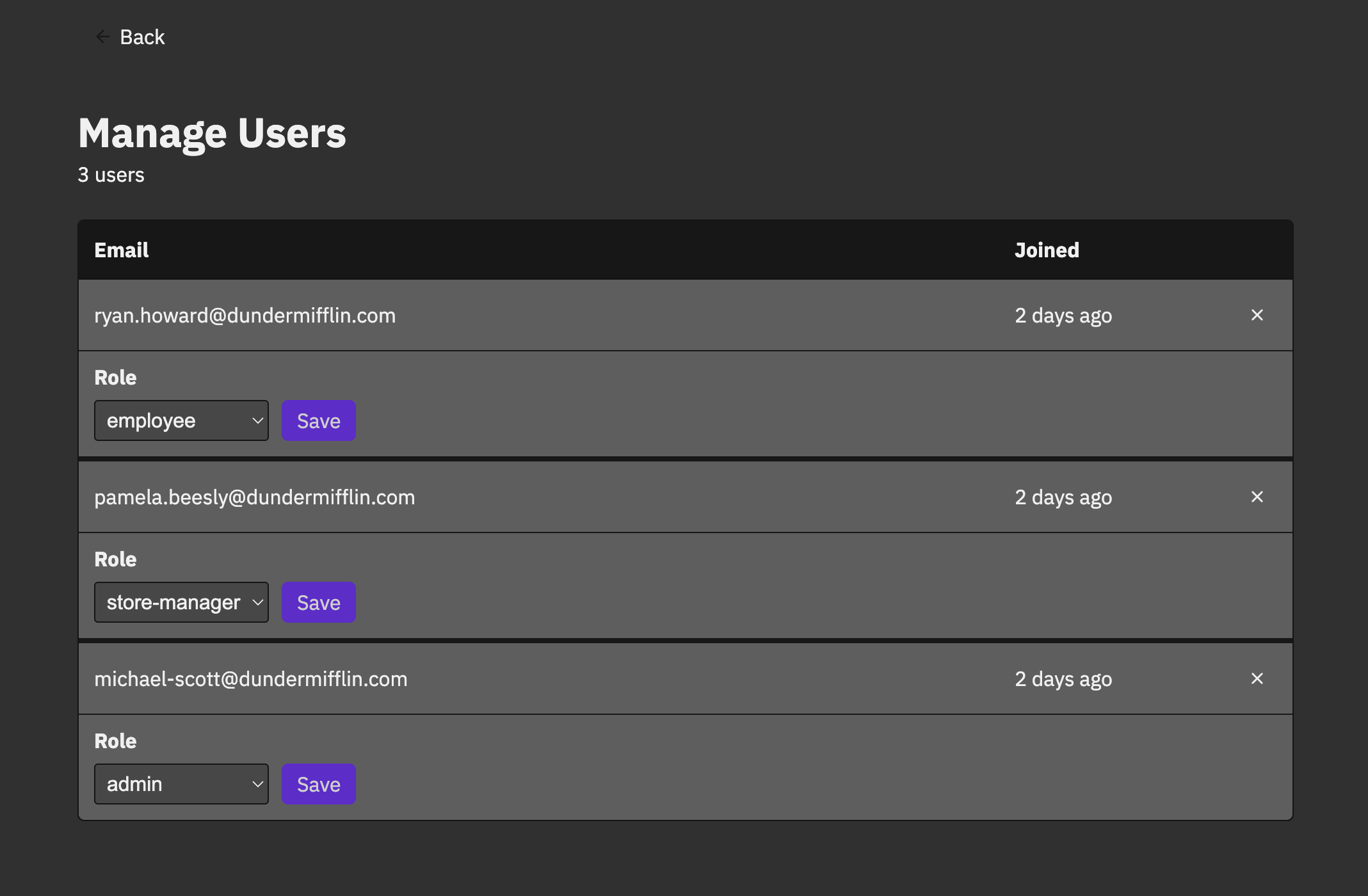
Org & Team Management
Fine Grained Access
Policy Based Access
APIs & Integrations
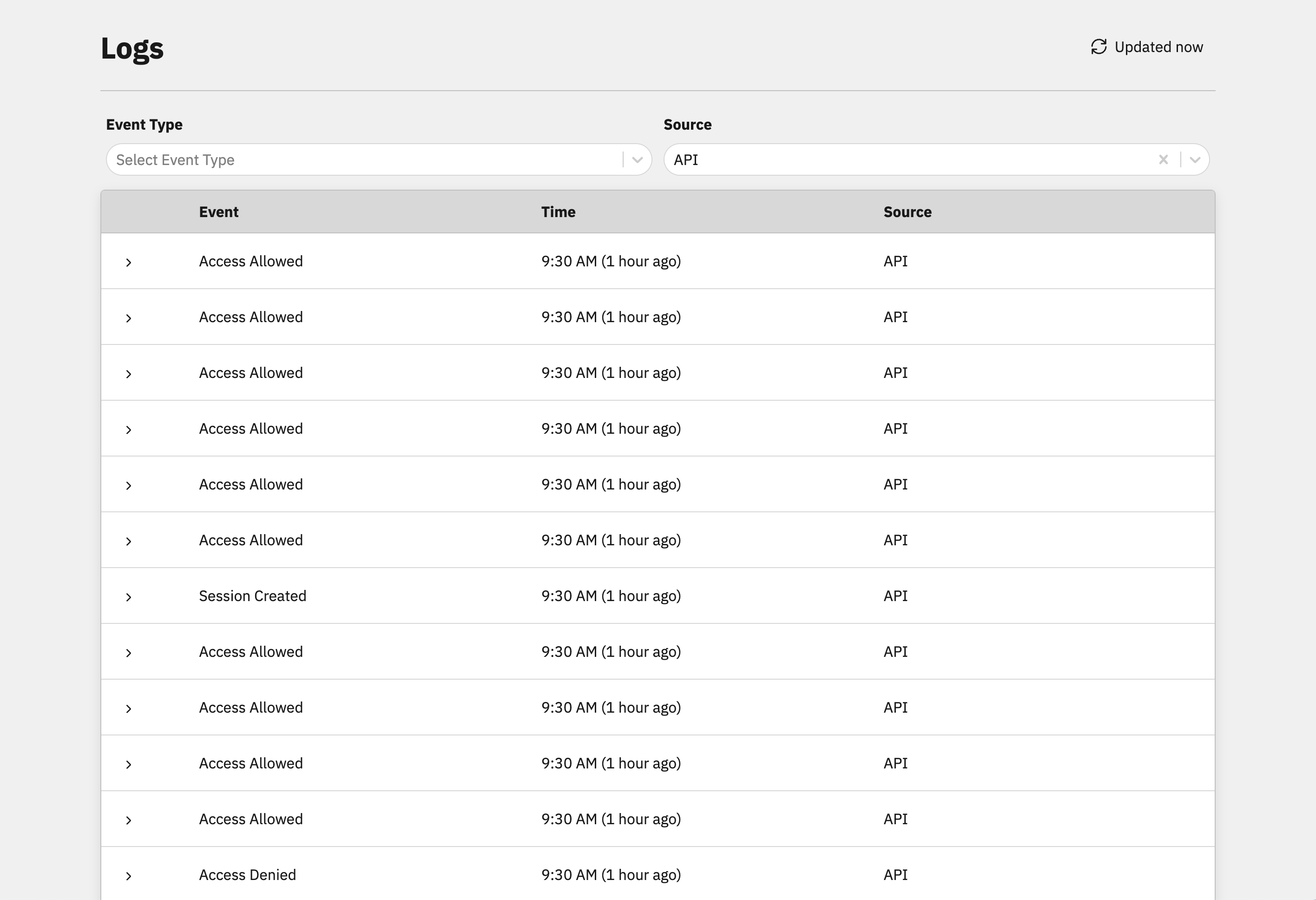
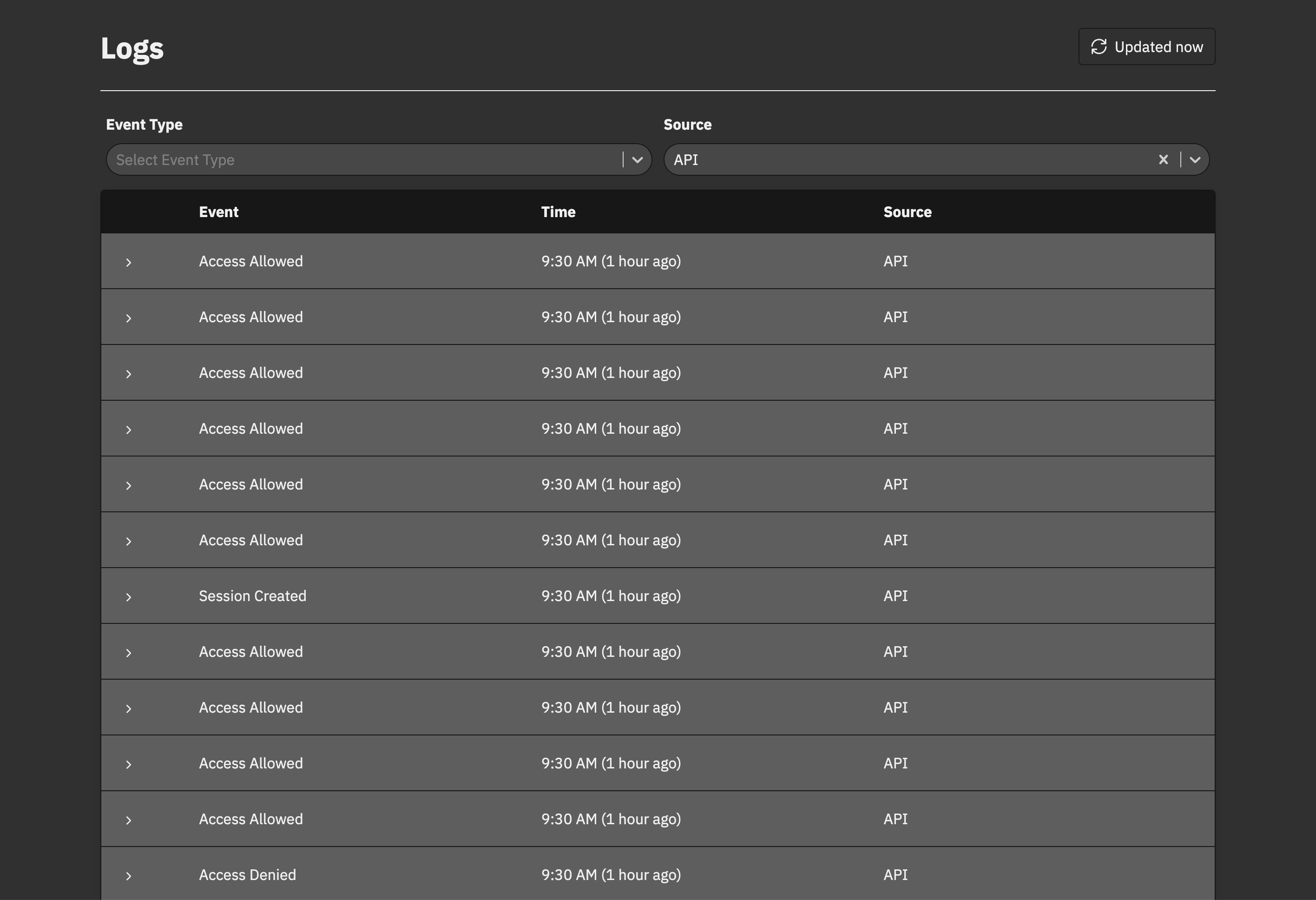
Audit Logs
Embeddable Components
Management Dashboard
No/Low Code Workflows
1{2 "type": "team",3 "relations": {4 "admin": {},5 "manager": {6 "inheritIf": "admin"7 },8 "member": {9 "inheritIf": "manager"10 }11 }12}
Model Permissions as Schema
Model any access control scheme from RBAC to FGAC & ABAC, or create a custom model that fits your use-case and requirements using object types.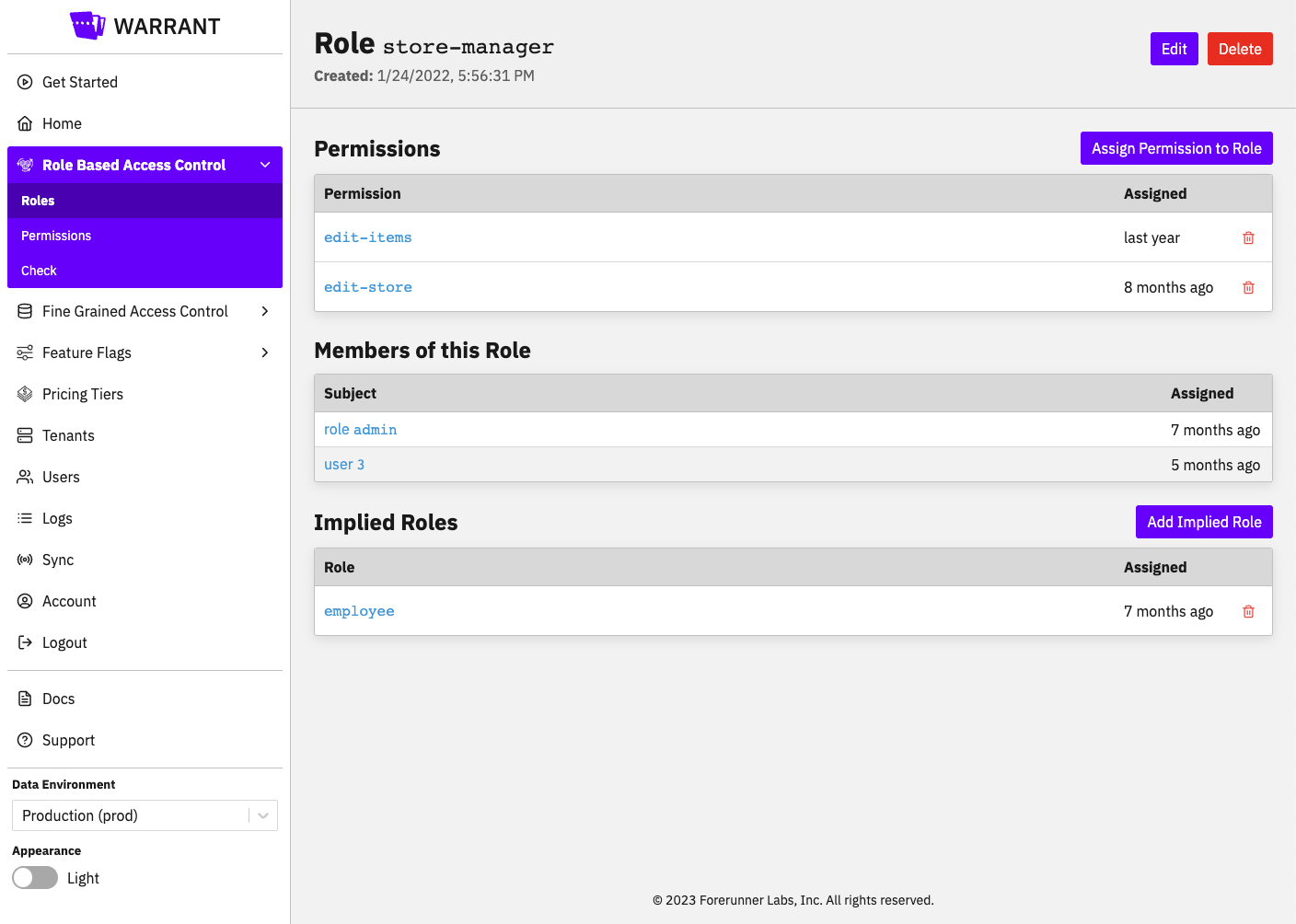
Management Dashboard
A management dashboard designed for use by developers, IT administrators, and even customer support & account managers makes it simple to manage employee and/or user access.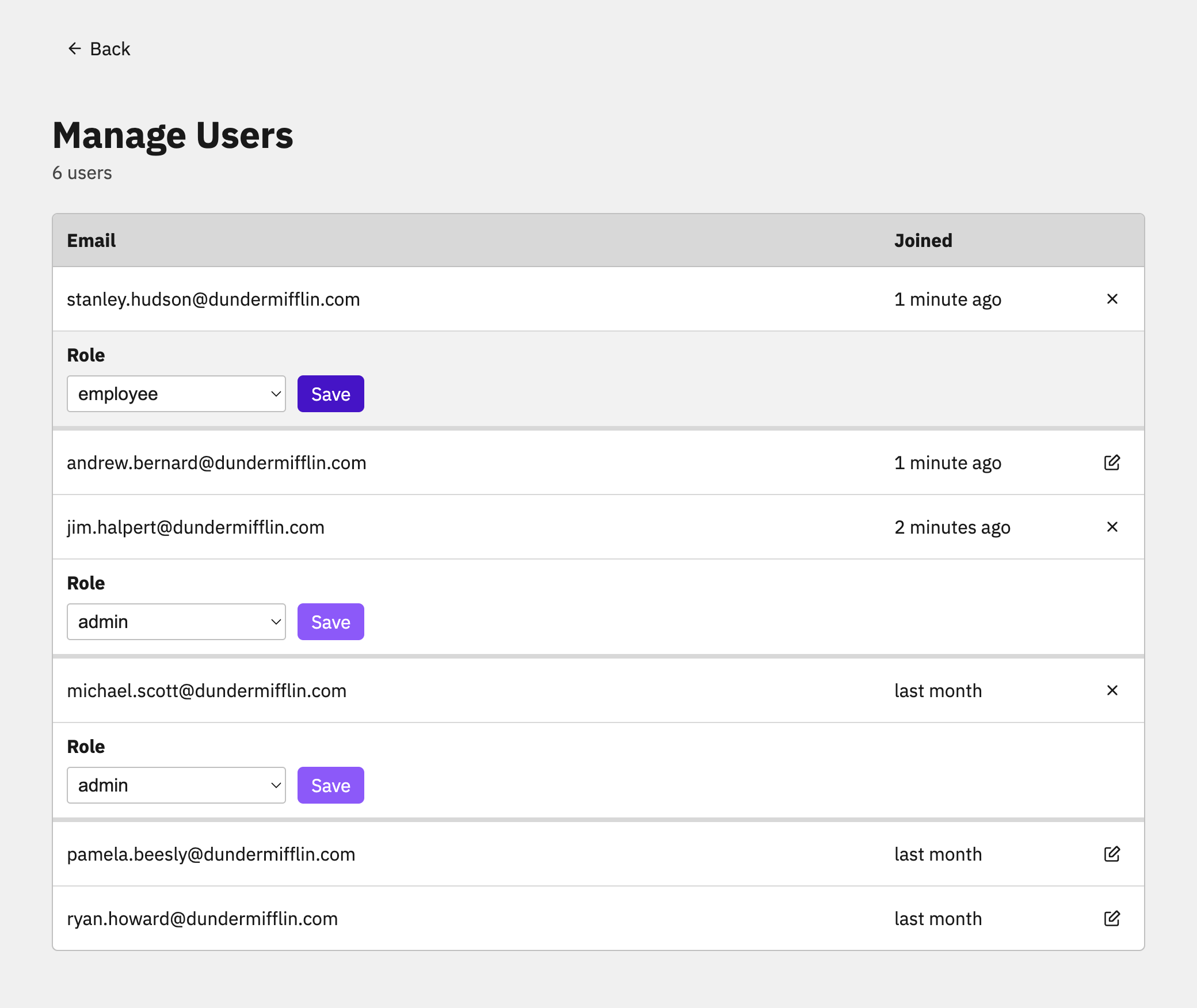
Low/No-Code Self-Service Workflows
Prebuilt, Warrant-hosted pages allow you to add delegated, self-service access management to any application with little to no code.